Two posts in a year, not bad 😛
Like a lot of companies that drink the Microsoft cool-aid I work for a place that uses Skype for business for text chat/voice communications… it generally works pretty well.
A few colleagues of mine have Blynclight status lights above their monitors as a visual indicator to visitors and/or other people around you that you are free/busy/uninterruptible. The concept itself looked pretty simple to build so I thought I’d give it a go… My project is called SkypeSignal (I’m not very good at names):
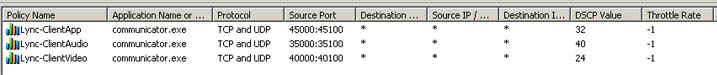
My solution comprises of two main parts:
- An Arduino nano connected to a couple of RGB LED lights
- A .NET application which uses the Lync client SDK to send commands to the Arduino via serial (over USB)
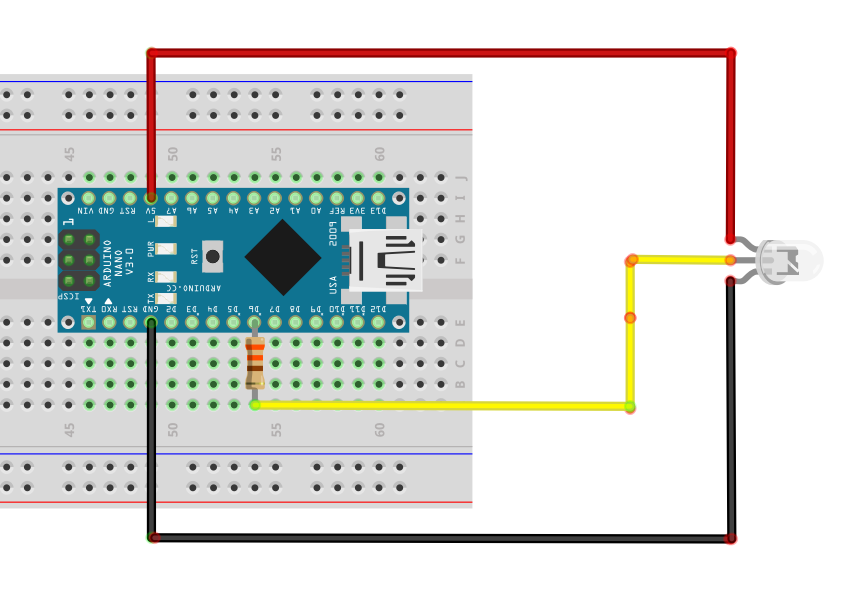
The Design:
The parts list for the actual build is pretty minimul:
- Arduino Nano
- A few RGB LED’s (supports a PWM driver [i.e. WS2811])
- a 330 Ohm resistor
- USB Cable
- Project box
- Wire
I went for LED’s using the WS2811 chip to drive them; this means that we only need 3 wires to run the whole thing, the below design can be modified to chain LED’s together and address them individually or alternativly run them as single LED’s by sharing the same digital input.
The operating workflow:
- Device connected to USB
- Relevant COM port set in SkypeSignal.exe.config and application started on PC
- A thread is started to run a small tray application on the windows task bar
- A thread is started to subscribe to Skype/Lync client events using the client SDK
- On client status change, a numerical command is sent down to the Arduino where it switches the light to the colour/pattern representing the presence of the user.
It would be trivial to add new features to this and I may look at adding some of these in the future:
- Have the .NET app send a PING to com devices and using device on com port that responds with expected value
- Flashing on missed notifications
- Strobe + Audio Alerts on Incoming call (I’ve included a speaker in my version for future use)
- Look at pulling the status over IP using UCWA to have a headless status device.
- Tidying up the code – its pretty janky
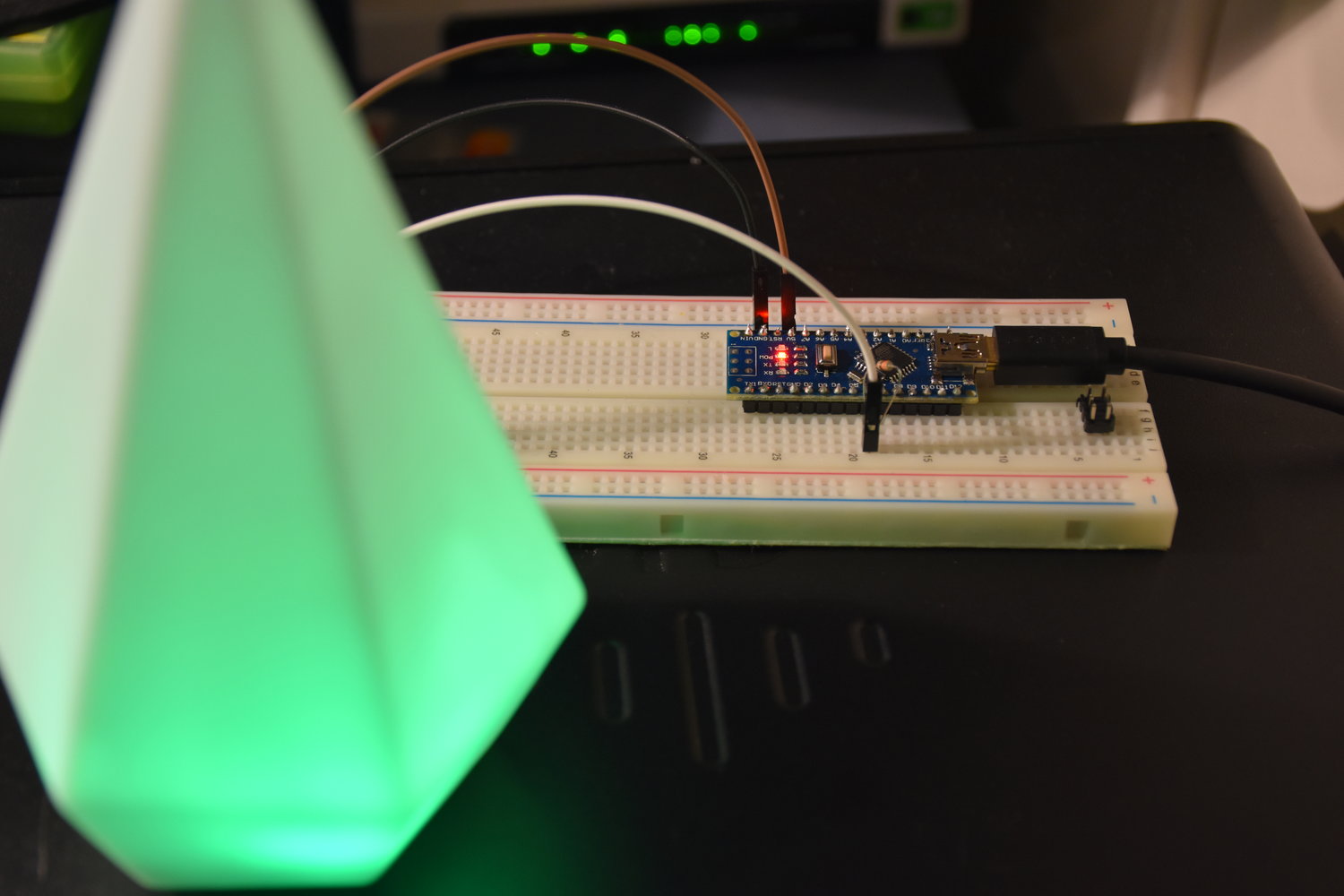
Demo:
The finished project above works pretty sweet – If you want a copy of the code, check it out in my Repo here: https://github.com/coaxke/SkypeSignal
Or download a copy at https://www.resdevops.com/files/binaries/SkypeSignal.zip
Drop me a line if you have any questions.
-Patrick
Edit:
Aug 17: I’ve just added incoming call alerts to the app (requires updates for tray-app plus Arduino sketch. Enjoy